IT Security Roles and Responsibilities
Well-defined roles and responsibilities are imperative for cross-functional DevSecOps teams. Teams shall adhere to these high-level roles and responsibilities. However, to support agility and based on the maturity of the team, these roles and responsibilities will be reviewed prior to each engagement. Mutually agreed-upon roles and responsibilities will be finalized between the Office of DevSecOps and the integrated teams.
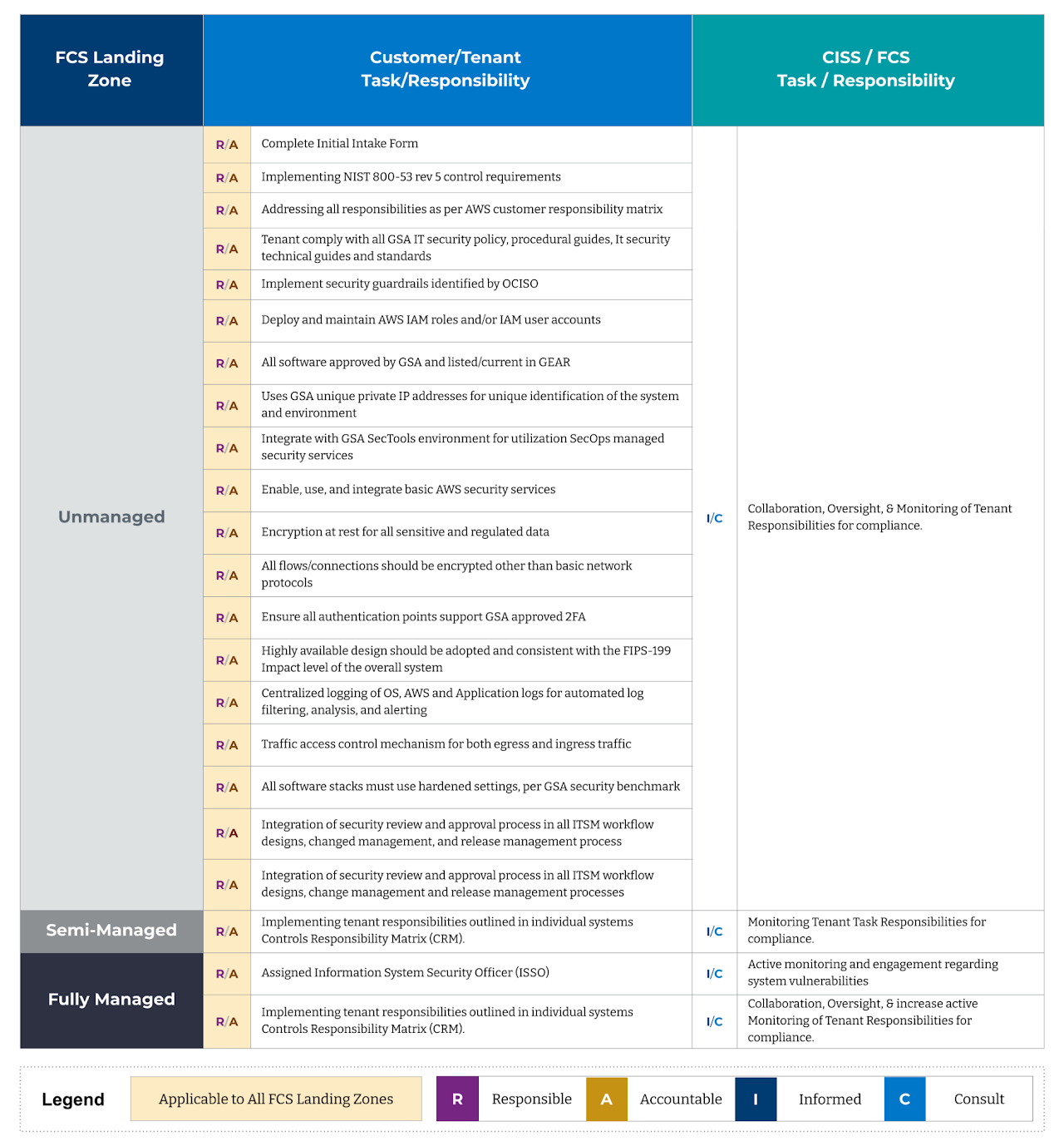
Landing Zone Roles and Responsibilities
General GSA IT Responsibilities
Roles & Responsibilities
- Authorizing Officials (AO) Responsible for authorizing the operation of all systems, networks, and applications for which they have responsibility. They may delegate some of their authority (e.g., the role of Authorizing Official in writing) to appropriately qualified individuals within their organizations.
- GSA Chief Information Officer (CIO) Has overall responsibility for the GSA IT Security Program. The CIO is responsible for providing guidance, assistance, support, and management processes to GSA staff and organizations to enable them to perform their responsibilities with regard to GSA's IT Security Program.
- Chief Information Security Officer (CISO) The focal point for all GSA IT security and must ensure the security requirements described in this Order are implemented agency-wide. The CISO reports directly to the CIO as required by FISMA.
- Information System Security Manager (ISSM)
Reports to the ISSO Support Division (IST) Director in the OCISO. There is at least one ISSM per AO. The ISSM is responsible for all IT system security and privacy matters for the systems under their authority. ISSMs are appointed, in writing, by the Director of IST with concurrence by the CISO. An individual appointed as an ISSM for a system cannot also be assigned as the ISSO for the same system. - Information System Security Officers (ISSO) Responsible for ensuring implementation of adequate system security, including privacy analysis/protection, in order to manage cyber-security risk aligned with the CSF functions of identify, protect, detect, respond, and recover. An ISSO must be assigned for every information system. An ISSO may have responsibility for more than one system, provided there is no conflict. An individual assigned as the ISSO for a system cannot also be the ISSM for the same system. ISSOs must be appointed via a designation letter. An ISSO must be knowledgeable of the information and processes supported by their assigned systems.
- System Owners (S/SO) Management officials within GSA who bear the responsibility for the acquisition, development, maintenance, implementation, and operation of GSA's IT systems. System Owners represent the interests of the system throughout its life cycle. Primary responsibility for managing risk rests with the System Owners. System Owners must ensure their systems and the data each system processes have the necessary security and privacy controls in place and are operating as intended and protected IAW GSA regulations and any additional guidelines established by the OCISO and relayed by the ISSO or ISSM.
**Note: In addition to the aforementioned high-level requirements, GSA showstoppers must be taken into consideration. Failure to address GSA showstoppers will preclude Authorization.


